Are you preparing for a network engineer interview? If so, you’re likely to be asked a range of questions about your experience, skills, and knowledge. In order to help you prepare, we have come up with the most asked commonly asked network engineer interview questions. If you are looking for Questions about networks you can visit here. And if you are preparing for Amazon Data Engineer Interview Questions you can visit here.
Network Engineer Interview Questions
We have divided these Network Engineer Interview Questions into two parts:
- General interview Question for Network Engineer
- Technical Network Interview Questions → Jump to these questions
General interview Question for Network Engineer
If you are preparing for a network engineer or system engineer job or internship, the following are some most common questions about network engineering:
1. What experience do you have in-network engineering?
This is one of the most asked questions in a network engineer interview. The interviewer wants to know your practical experience in managing, designing a network and troubleshooting networks. Give examples of specific projects you’ve worked on and challenges you’ve overcome.
2. What inspired you to become a network engineer?
The interviewer wants to know what motivated you to enter this field and pursue a career in network engineering. Be honest and share your story. Perhaps you were always interested in computers and technology, or maybe you had a positive experience working with networks in a previous job. Whatever the case, be sure to emphasize your passion for the field.
3. What are the biggest challenges facing network engineers today?
This question allows you to showcase your knowledge of current trends and issues in the field. Be sure to mention specific challenges, such as increasing data traffic, the proliferation of IoT devices, and the need for faster and more reliable networks.
4. What is the most important skill you have regarding Networks?
There are many important skills that a network engineer needs, but the interviewer wants to know which one you think is the most important. You might want to mention technical skills like experience with networking or routing protocols or the ability to use network analysis tools. You can share the experience of managing different platforms and vendors like Cisco, Huwaei etc. Alternatively, you could highlight soft skills like problem-solving or teamwork. Whatever answer you give, be sure to back it up with examples.
5. What do you think sets your skills apart from other network engineers?
This is your chance to sell yourself and you can explain your extra certification regarding networks, the management or leadership skills to show that you can be part of any good organization. Be confident in your answer and list specific examples of your skills and experience that make you stand out.
6. What is the most successful project you have worked on?
This question allows you to showcase a specific example of your skills and experience in action. Be sure to give details about the project, including what your role was, what challenges you faced, and how you overcame them.
7. What has been the biggest failure in your career so far?
This question will test your ability to learn from your mistakes. Be honest in your answer and describe what happened, what you could have done better, and what you learned from the experience.
8. What do you think is the biggest challenge you’ll face in this role?
The purpose of this question is to test if you are prepared for the challenges of the job. This is an excellent opportunity to ask clarifying questions about the role and expectations. Once you have a better understanding, share your thoughts on what you think the biggest challenge will be and how you plan to overcome it.
9. What’s your troubleshooting process?
Be sure to walk the interviewer through your step-by-step process for troubleshooting network issues. Include details on how you collect data, identify the root cause of the problem, and implement a solution.
10. What do you think has been the most challenging issue you’ve faced with a network?
The interviewer wants to know if you’re able to handle difficult challenges. Share a specific example of a complex issue you faced and how you successfully resolved it. This will show that you have the skills and experience required to excel in this role.
11. What is your view about network security?
Network security is a critical issue for all businesses, so you must have a strong stance on it. Share your thoughts on the importance of network security and describe your process for ensuring that networks are secure. Include details on identifying potential threats, implementing security measures, and monitoring networks for suspicious activity.
12. What has been the most challenging network to troubleshoot? Why?
This question allows you to showcase your problem-solving skills. Share a specific example of a complex issue you faced and how you successfully resolved it. The interviewer will judge your skills and experience fit for a new role or not.
13. Describe a network issue you dealt with and how you solved it?
A good way to answer this quest is to share your troubleshooting skill regarding computer networks. You can talk about any LAN or WAN issue you face in past. Be sure to walk the interviewer through your step-by-step process for troubleshooting network issues. Include details on how you collect data, identify the root cause of the problem, and implement a solution.
14. What do you think is the most important skill for a network engineer to have?
There are many important skills that a network engineer needs, but the interviewer wants to know which one you think is the most important. You might want to mention technical skills like experience with networking protocols or the ability to use network analysis tools. Alternatively, you could highlight soft skills like problem-solving or teamwork. Whatever answer you give, be sure to back it up with a specific example.
15. Why should we hire you as a beginner?
If you are a beginner then this question allows you to show your motivation for the job. You need to research the company and the role before the interview so you can tailor your answer to their needs. Focus on sharing your skills and experience that make you a good fit for the job and how you would contribute to the company’s success.
Technical Network Interview Questions
16. What is the OSI reference model?
The OSI reference model is a seven-layer model that defines the standard for transmitting information between devices on a network. The seven layers are physical, data link, network, transport, session, presentation, and application.
17. What is the difference between half-duplex and full-duplex?
In Half-duplex communication, both devices can not communicate simultaneously, each device can communicate n one direction at a time, whereas in full-duplex communication can happen in both directions simultaneously.
18. What is the backbone network?
The backbone network is the main network that connects all the other networks. It is typically made up of high-speed links and routers.
19. What is the single biggest advantage of using a network?
Networks offer many advantages, but the interviewer wants to know which one you think is the most important. Some possible answers include increased communication, collaboration, and productivity; easier sharing of data and resources; and improved security.
20. What is a LAN?
LAN stands for local area network. It is a computer network that connects different devices which are existing in the same building, such as a home, office, or school. With a Local area network, you can enable access to different applications, and sharing of services, devices and files.
21. What is data encapsulation?
Data encapsulation is the process of wrapping data in a layer of security, such as encryption. In networks, every layer is receiving the data from upper layer and sends in the packet or frame. Encapsulation protects your data from unauthorized access.
22. What is the difference between a hub and a switch?
A hub connects devices on a network and allows them to communicate. A switch is a more sophisticated device that connects devices on a network and controls the data flow between them.
23. What is the difference between a router and a gateway?
A router is a device that can enable communication between two or more networks or LANs. A gateway is an exit point or endpoint that provides access to another network, such as the Internet. In networks normally we route all the traffic or request of unknown networks to the default gateway.
24. What are the three types of network topologies?
The three types of network topologies are bus, star, and mesh.
25. What is the single biggest disadvantage of using a network?
Some possible answers to this question include increased complexity, the potential for security breaches, and reliance on network infrastructure.
26. Briefly describe NAT?
NAT stands for Network Address Translation. It is a method of mapping one IP address to another. This allows devices on a private network to use a public IP address.
27. What is the difference between a public and private IP address?
A public IP address is a global address that can be accessed from anywhere on the world/Internet. We used public IP access to make the devices or services accessible on the internet. The private IP addresses are used in LAN to enable internal communication.
28. What is the difference between a static and dynamic IP address?
When we assigned a permanent IP address to any network device, it is called a static IP address and it does not change. A dynamic IP address is normally assigned by DNS and these addresses keep changing according to the available DNS pool. Check out our related post on DNS Interview Questions
29. What is the default gateway?
The default gateway is the network device forwards data packets from one network to another.
30. What is the subnet mask?
The subnet mask is a 32 bits value that is used to determine the portion of an IP address that represents the network and other bits are used to represent the host part.
31. What is an IP address?
All network communication is based on the IP address. An IP address is a unique address which is assigned to every device on a network. The network administrator typically assigns it. You can learn more details about the what is IP addresses here.
32. What are the three types of cabling used in networks?
The three main types of cabling used in networks are twisted pair cable, coaxial cable, and fiber optic.
33. What is RIP?
RIP is a routing protocol used to connect two or more networks. Routing information protocol is a distance-vector protocol and it can work up to 16 hop counts. You can visit here to learn why to use routing information Protocol.
34. What is OSPF?
Open shortest path first is a protocol used to exchange routing information between devices on a network. OSPF works best in WAN environments, and it used the Dijkstra algorithm to find the shortest part. You can learn more about the Open shortest path first protocol here.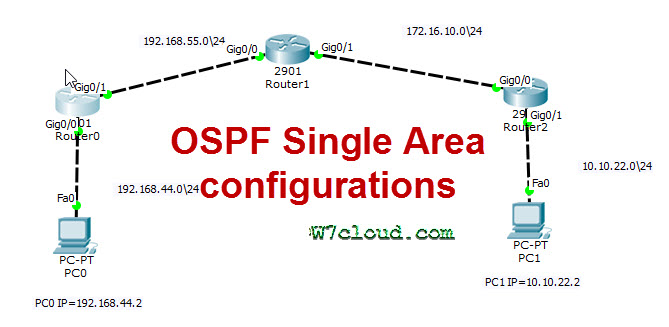
35. What is BGP?
BGP is a routing protocol of the internet used by internet service providers to connect the different ISPs on the internet. You can learn a short brief about BGP here.
36. What is the difference between layer 2 and layer 3 switches?
A layer 2 switches forward data based on the MAC address of the devices on the network. A layer 3 switch used the IP address to forward the data based on the network.
37. What is the difference between a router and a switch?
One of the main differences between the two is that the router can connect the two different networks, a router forwards data packets based on IP addresses between networks. On the other hand, a switch uses to connect the devices with the network and forwards the packets between devices on a single network using the MAC address.
38. What is the difference between a layer 2 and layer 3 network?
A layer 2 network is a network that uses MAC addresses to forward data. A layer 3 network is a network that uses IP addresses to forward data.
39. What is the difference between an intranet and an extranet?
An intranet is a private network that authorized users can only access. An extranet is a private network that authorized users and external partners can access.
40. What is the difference between a VPN and an intranet?
A Virtual private network is a private network that uses to connect the two public networks using a secure tunnel within the internet. An intranet is a private network that authorized users can only access. You can learn more about what is a virtual private network.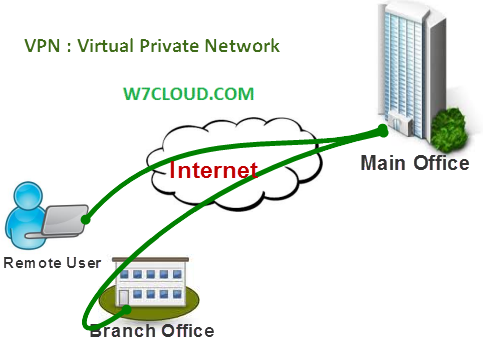
41. what is native VLAN and why do we use these?
Native VLAN is the VLAN where untagged traffic will be forwarded. The reasons to use native VLAN are:
– It keeps the traffic separated from other VLANs
– To improve the performance
– You can simplify the configuration using Vlans
42. Is native VLAN necessary?
No, native VLAN is not necessary. It can be used to improve the performance and simplify the configuration, but it is not required.
43. What is a MAC address?
MAC addresses are the physical address that a network device use for communication on the LAN. The manufacturer of the device typically assigns them.
44. What is the difference between a unicast, broadcast, and multicast address?
A unicast address is an address that is assigned to a single device. A broadcast address is an address that is assigned to all devices on a network. A multicast address is an address assigned to a group of devices.
45. What is the difference between a Class A, Class B, and Class C IP address?
A Class A IP address is an address that any device can use on the Internet. The Class B IP address is an address that any device can use on a private network. Whereas the Class C IP address is an address that devices can only use on a specific private network.
46. Why do we need a firewall?
Firewalls protect the networks from different attacks and unauthorized access. You can enable different rules by using the firewall to block or allow traffic from any protocol, port or from a specific IP address.
47. Is firewall hardware or software?
Firewalls can be hardware or software. Hardware firewalls are typically physical units, which have different ports for traffic in or out where you can filter the traffic. Hardware firewalls are used to protect large networks. Whereas Software firewalls are the applications or software which are usually used to protect individual devices.
48. Name some of the popular firewall vendors?
Some of the popular firewall vendors are Cisco, Juniper, and SonicWALL.
49. What is the difference between a stateful and stateless firewall?
A stateful firewall keeps track of the state of each connection. A stateless firewall does not keep track of the state of each connection.
50. What is the difference between STP & RSTP?
Spanning tree protocol is a protocol that is used to prevent loops in a network. It is the Cisco proprietary protocol which detects the loop in the switch environment and in case of a loop STP automatically blocks one port to avoid the loop. RSTP is an improved version of STP that is faster and more efficient. You can check out the STP interview Questions and answers here.
51. What is the difference between a hub, switch, and router?
You can connect multiple devices with the Hub. But a hub is a device with a single collision domain which means that only one device can send and receive the data at a time. On the other hand, a switch is a multiple collision device which means multiple devices can send or receive the data at the same time. A router is a device that connects multiple networks and routers forward on the basis of the packet on the IP address.
52. What is the difference between IPsec and VPN?
IPsec is a protocol that is the set of security protocols used to secure communication between the 2 nodes. IP sec works on the network layer and is used for the protection of data across the VPN. Whereas a VPN is a private network that creates a secure connection between two remote nodes.
53. What is IPsec VPN?
IPsec VPN is a type of VPN that uses IPsec to secure communication between two devices.
54. What is an Active Directory used for?
Active Directory is used to store and manage user information. It can be used to authenticate users and authorize access to resources. you can check out our post-related active directory.
55. What does a network engineer do?
Responsibilities of a network engineer include designing and implementing network infrastructure, troubleshooting network issues, and managing network security. They play a very major role in monitoring network performance and providing support to users.
Network engineers also monitor security systems and ensure network availability to users. They also work on optimizing the network to increase network efficiency and speed.
One of the network engineers’ main tasks is creating documentation for the network. This documentation includes IP addresses, device configuration, and network diagrams. This documentation is important for troubleshooting and future reference.
56. What are the skills required for a network engineer?
A network engineer requires strong analytical and problem-solving skills, experience with network design and implementation, and knowledge of network protocols and technologies. The network engineer must have ability to work independently and be able to troubleshoot complex problems.
57. What’s the largest network you’ve managed?
I’ve managed networks with up to 1000 devices. When I was working in the previous company, there were three internet offices across the world and these are connected via BGP and whereas on LAN we have different services like exchange server, active directory, ISA server, web server and FTP server etc. So there I have worked to troubleshoot different WAN and LAN issues and it was a great experience for me.
58. How would you begin scaling an organization’s network?
The first step you need to consider the current network infrastructure and identify any bottlenecks. Once the bottlenecks have been point out, you need to take steps to resolve these issues. This may involve adding additional devices or increasing the bandwidth of existing devices.
59. What do you think is the most difficult problem with network security?
There are many problems with network security, but one of the most difficult is preventing data breaches. Data breaches can occur due to various factors, such as malicious attacks, human error, or system vulnerabilities.
60. What is the most important factor to consider when designing a network?
Security is one of the most important factors to consider when designing a network. The network must be designed in such a way that it can withstand attacks and protect the data of the organization.
61. What is the most difficult problem with network administration?
If you asked me the most difficult problem of network administration is the extension of network or managing changes to the network. Changes to the network can occur due to a variety of factors, such as new applications being deployed, system updates, or changes in user needs.
62. What kind of experience with network analysis do you have?
I have experience with both network and application-level analysis. I’ve used various tools to perform analysis, including Wireshark, NetFlow, and packet capture devices.
63. What is the most important factor to consider when troubleshooting a network issue?
The most important factor to consider when troubleshooting a network issue is identifying the root cause of the problem. Once the root cause has been identified, steps can be taken to resolve the issue.
64. What is the most difficult problem with network management?
One of the most difficult problems with network management is dealing with unplanned changes to the network. Changes to the network can occur due to a variety of factors, such as new applications being deployed, system updates, or changes in user needs.
65. Is GPON better than Ethernet?
There is no definitive answer to this question as it depends on the organization’s specific needs. GPON may be a better option for organizations that require high bandwidth and low latency, while Ethernet may be a better option for organizations that require lower costs.
66. What is the difference between Outlook and Exchange Server?
Outlook is a client application that connects to Exchange Server. Exchange Server is a server application that stores and manages email messages, contacts, and calendar items.
67. Share your experience regarding the Exchange Server?
I have experience working with Exchange Server 2010 and 2013. I am responsible for managing the server, including creating mailboxes, configuring mailbox permissions, and managing email routing.
68. What is the biggest advantage of using VoIP?
The biggest advantage of using VoIP is that it can significantly reduce phone call costs. VoIP uses the Internet to make phone calls, so there are no long-distance charges.
69. Is BGP TCP or UDP?
BGP is a TCP-based protocol. This means that it uses the TCP/IP protocol to establish a connection with another BGP router and exchange routing information.
70. which is better, cisco VOIP or Huawei VOIP solution?
There is no definitive answer to this question as it depends on the organization’s specific needs. Cisco VoIP may be a better option for organizations that require high quality and reliability, while Huawei VoIP may be a better option for organizations that require lower costs.
71. how can you evaluate networking products?
There are several factors to consider when evaluating networking products. These factors include performance, scalability, reliability, and cost.
72. What are the administrative distances, and tell the administrative distances of different routing protocols?
Administrative distance is a metric used by routers to determine which routing protocol to use when multiple protocols are available. The administrative distance of a protocol is defined as the measure of the trustworthiness of the protocol.
Different routing protocols have different administrative distances. For example, the administrative distance of OSPF is 110, while the administrative distance of BGP is 20.
73. What do you think of the Open Systems Interconnection (OSI) model?
The OSI model is a conceptual model that defines how information is exchanged between devices on a network. The model is divided into seven layers, each representing a different aspect of the data exchange process.
74. What is routed and routing protocol?
A routed protocol is a network protocol that uses a network layer. A routing protocol is a protocol that defines how routers exchange information about routes. Examples of routed protocols are IP, IPv6, and AppleTalk. Examples of routing protocols are OSPF, BGP and RIP.
75. what are VTP and the purpose of VLAN trunking protocol? Share an example?
VTP is a protocol that allows multiple switches to share VLAN information. The purpose of VTP is to simplify the management of VLANs. VTP allows a network administrator to create, modify, and delete VLANs on all switches in a VTP domain.
For example, if a network administrator creates a new VLAN on one switch, that VLAN will be automatically created on all other switches in the VTP domain.
76. what is stp, how it prevent switching loops and share your experience working with STP?
STP is a protocol that prevents switching loops. STP does this by creating a logical topology of the network and then using that topology to calculate the best path for
A hub is a device that connects multiple devices and allows them to communicate with each other. A switch is a device that connects multiple devices and allows them to communicate with each other. However, a switch only allows communication between devices connected to the same switch.
77. what is subnetting? Share your experience working with subnetting?
With Subnetting, you can segment your network into smaller networks. Subnetting allows an administrator to control traffic better and manage the network. Subnetting also helps to improve security and reduce the chances of broadcast storms.
78. what is the primary benefit of using a routed protocol?
Routed protocols offer several benefits, including connecting multiple networks, improved performance, and increased security.
79. What Is Ris? What Is Imaging and ghosting and what are its advantages?
Ris is software that allows you to create images of your hard drive. Imaging allows you to take a “snapshot” of your hard drive, which can be used to restore your system if it becomes corrupt or damaged. Ghosting is similar to Imaging, but it allows you to create an exact copy of your hard drive. Ghosting can be used to clone your hard drive or to create a backup.